I am going to share with you a funny but serious event that unfolded in my Inbox yesterday. There is a silly job listing site in the name of jobszone.info. They blast bulk mails to thousands of people about latest job openings. Yesterday I received a mail from them that reads.
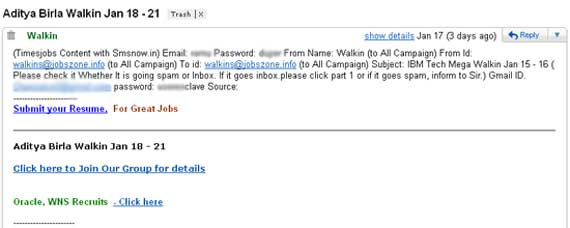
Now what does a user like me do in this case. Carelessness like this leads to the hacking of email accounts and corporate websites.
Here is how a hacker would proceed once he is fed with information like this. I am not a hacker but I have read about them and I am somewhat familiar with their train of thought. Thanks to recent events like Iranian attack on Twitter.and previous Twitter Admin hack news.
So first of all we try out popular mail portals like Gmail, Yahoo, Hotmail, AOL etc. If our trial yields no result then we try to access the webmail accounts using urls like domain.com/webmail or mail.domain.com. How to find out the site? Use google for the most relevant term from the mail. It is not always that easy though.
In my case I struck gold with Gmail. Though I tried the domain.com/webmail approach first as the mails seemed to originate from the said website.
Normally what first timers would do is reset the password. But that is the stupid thing to do. Don’t let the original user suspect that the account has been compromised.
Next search for password or username using mail accounts search feature. Gmail in this case is just wow. I got around 40 results. This idiot left an excel file with a list of user ids and passwords for some 25 accounts. Wow. I can further use the same to get into more classified information. May be I could find some credit card details too but my ethics stop me going beyond this. LOL
Additionally one could use Gmail labels or folders in other email clients to reach out to specific information on your email accounts.
I hope this malicious email account access process would give you enough ideas about how to protect your accounts from being hacked. Many large organizations like twitter have been hacked using this very method.
This has been a long post already. Watch out for my next post that is a list of steps to keep your accounts safe from hacking.


now when is your damned second part coming up