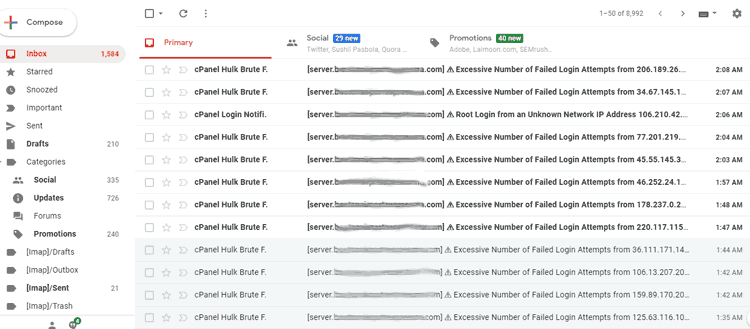
Do you receive 100s or emails every day like that shown below? My inboxes used to be filled with such emails every hours. It was maddening when I used to get 800+ emails a day. Finally, I solved the problem with a little research. I am sharing the procedure to secure your server from Brute Force attempts and keep your inbox clean.
What is Brute Force? What is Cpanel Hulk?
Brute force is a method of hacking using a programmatic approach of guessing the password using a continuous trial and error method till the right password is guessed. It becomes easier when the username is commonly known and the password is relatively easy to guess. 81% or hackings succeed due to weak passwords or commonly used passwords.
Canel Hulk is an anti Brute Force protection software used by Cpanel/WHM server management tool to defend your server against Brute Force attacks as explained above. It comes free with your Cpanel/WHM license. It blocks an user by identifying its IP address, when the number of failed login attempts exceed a predefined number. (generally 5 attempts)
Why am I getting these Emails?
You are receiving these emails because you are are an admin or manager of a Cpanel/WHM account which is secured from BruteFore attacks. You are getting too many emails because you are currently under a Brute Force attack or SSH attack which aims at breaking the password of your Cpanel / WHM primary login – root user or other users.
In my case I have seen multiple attacks from users – root, admin, Ying, administrator etc. In one case all the attacks were via Shell Access or SSH. I am a Tech Consultant and I manage web development and Digital Marketing for many corporations around the world.
How to solve the Brute Force – Cpanel Hulk notification email problem on your server?
Here are the three main steps to follow to fix this problem
- First Check where the attacks originate from? Are they from a particular IP or a range or IP or a particular country? In that case use the suggestions links in the email to block the offending IPs, IP ranges or countries from WHM.
- Second, If the IPs are totally different and you cannot blacklist IP one by one (which is a wrong approach) check if what is the user name that is used and the type of service used to login. If the user name is “root” and if the service is SSHD then you have to Block the Root User Login privilege in Server Configuration.
- If there are brute forcing attempts from different user names, consider changing the SSH ports altogether which make it hard for the hackers to connect via SSH.