If you landed on this post dealing with Phishing scam on WordPress sites of Hostgator / Bluehost or custom made PHP sites because you might also have received a warning from your hosting company to “suspend your hosting” account. In this post we will address how to deal with such scams and hacking attacks.
Symptoms of the Raiffeisen Bank Phishing Hack
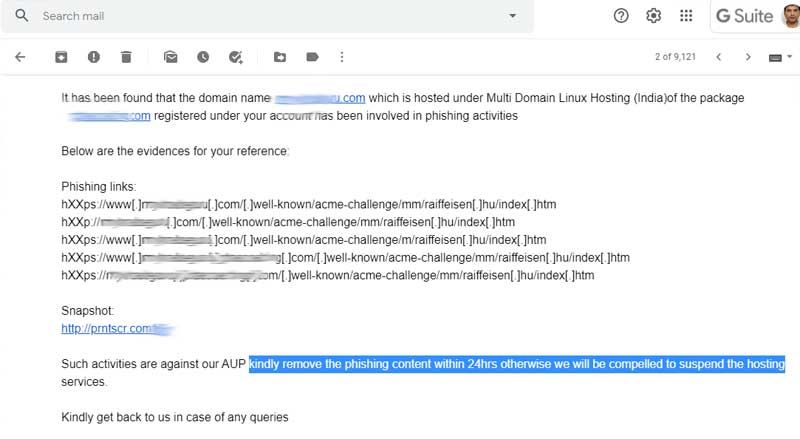
In most situations the victims never know this unless they are notified by the hosting company. You may get a warning email where you get a strict deadline to clear the malicious code from your website or face suspension.
Or you may also have noticed new URLs in your Google Webmaster tools or might have received warning in your Webmaster console regarding hacking or phishing issues.
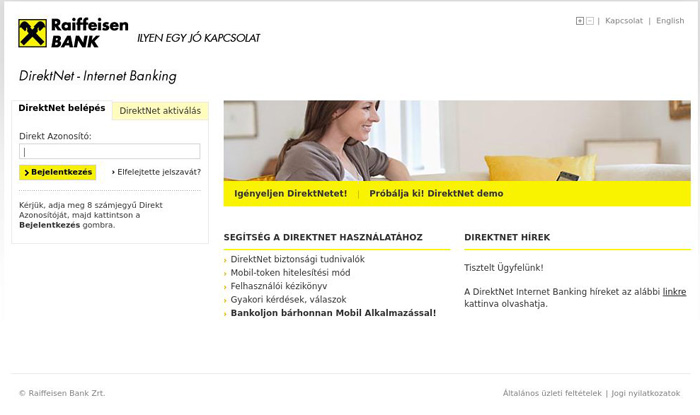
Basically, the issue is caused due to some malicious hackers who have broken into your website though security loopholes and built pages on your site that are an identical replica of some other sites. In this case some hacker has replicated the look of the Netbanking login page of Raiffeisen Bank and using it to dupe people. The pages may look something like this.
How to fix this and protect your Hosting account?
- Normally the first thing you should do is to contact your hosting company and request them for a hacking / malware attack security scan on the website. They won’t do it otherwise if they don’t feel that its a serious need. When they complete the scan they will provide you with a list of infected files you need to delete. Refer to the email screenshot above.
- Then login to your Cpanel or Hosting Manager and go to the File Manager section. It might be in the /.well-known/acme-challenge directory. Look for the following files and delete them completely.
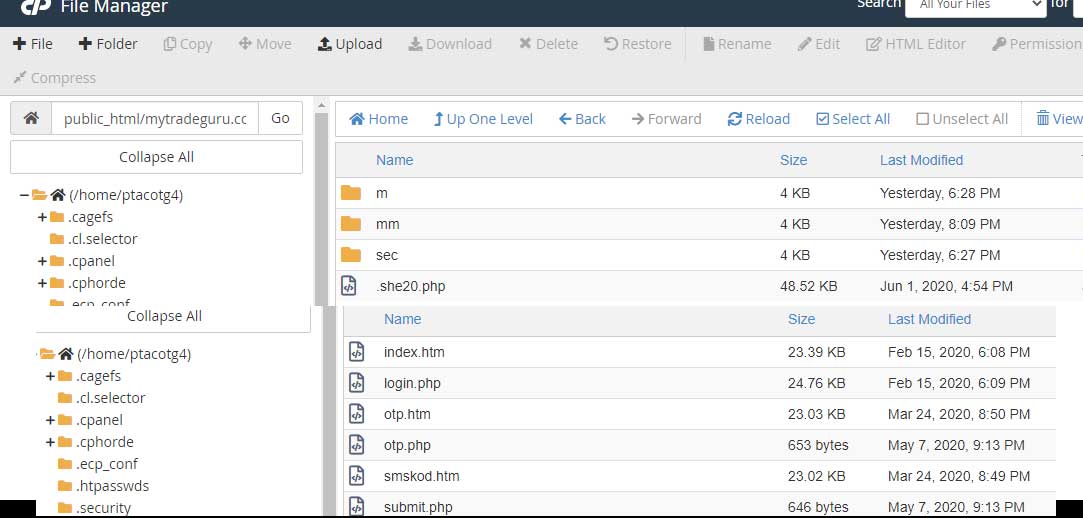
- After that search the entire hosting accounts for file names like otp.php or login.php or smskod.htm to find if more such files exist in other directories of the site.
See the example below on how searching for one of the infected file names helped me find out where else the infected files have copied themselves.